How to create an PFX file
A PFX file indicates a certificate in PKCS#12 format; it contains the certificate, the intermediate authority certificate necessary for the trustworthiness of the certificate, and the private key to the certificate. Think of it as an archive that stores everything you need to deploy a certificate.
You can create a private key together with the CSR, but you have to save it on your own (for later installation of the certificate). Your browser will offer private key download automatically.
When do you need to create a PFX? Most common scenarios
- You will install the certificate on Windows Server (IIS), but the CSR request was not created in IIS.
- You need a certificate for Windows Server, but you do not have IIS to generate the CSR.
- You created the CSR in SSLmarket and saved your private key. You now need to deploy the certificate to Windows Server.
Here is a guide for these (and other) situations.
Creating PFX using OpenSSL
OpenSSL is a library (program) available on any Unix operating system. If you have a Linux server or work on Linux, then OpenSSL is definitely among the available programs (in repository).
In OpenSSL, separately stored keys must be used in a single PFX (PKCS#12) file. So join existing keys to PFX:
openssl pkcs12 -export -in linux_cert+ca.pem -inkey privateky.key -out output.pfx
When you enter the password protecting the certificate, the output.pfx file will be created in the directory (where you are located).
Creating PFX on Windows (server with IIS)
Create a PFX from an existing certificate
From a Windows operating system, an existing certificate can be exported from the certificate store as a PFX file using the MMC. You can also choose to do this on a Windows server if IIS stores them in the certificate store.
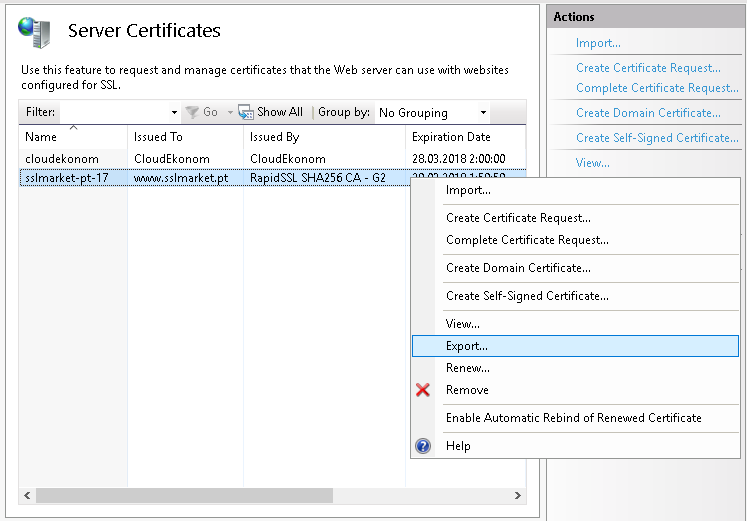
The IIS Web Server allows you to export an existing certificate to PFX directly from the server certificate store. The private key and CSR are created during the creation of a CSR request in IIS and the certificate is reimported when issued (both steps can be found in the video guide ).
Exporting is very simple - right-click on the certificate and select Export. After you choose a password to protect the PFX file, it is saved to disk.
Import a new certificate and create a PFX
Unfortunately, this is not possible. The Windows certificate store does not allow you to import a separate private key from a file, so in MMC you do not merge keys to PFX as in OpenSSL. You can only import PFX into an IIS web server, so what is in the previous case.
If you need to import a new certificate into Windows Server and there is no private key on the server (you did not create a CSR request on the server), you can follow these steps:
- Create PFX elsewhere (OpenSSL or otherwise) and then import the certificate using PFX
- Create a new CSR request on the server and perform a reissue of the certificate.
Create a PFX using a third-party application
You can create a .pfx file from separate keys in a graphics program to bypass the need to use OpenSSL in the terminal.
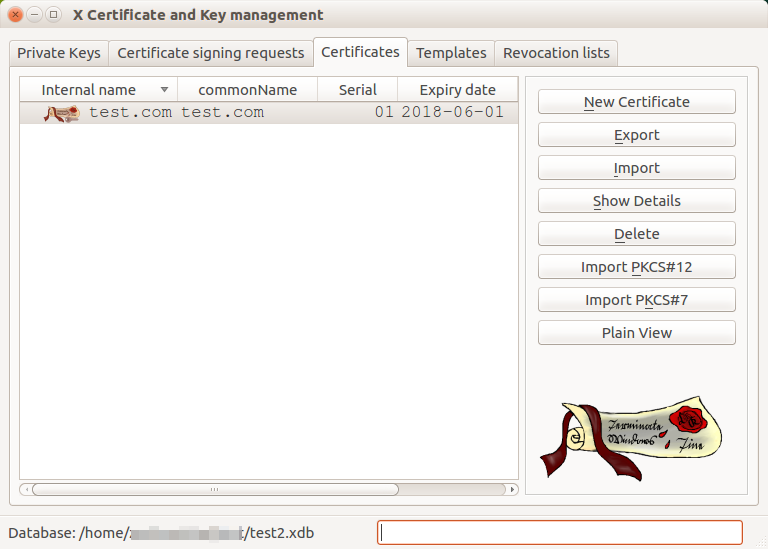
The best program for this purpose is opensource XCA. In this intuitive program you can manage all your certificates and keys. The main advantage is the automatic matching of the corresponding keys to each other; you do not have to look for which private key belongs to which certificate. Importing keys is easy and you can export to all known formats.
(In)security of the PFX file
The PFX file is always password protected because it contains a private key. When creating a PFX, choose a password responsibly, as it can protect you from misuse of the certificate. An attacker would be pleased if the password to the stolen PFX file was "12345" - he could start using the certificate all the time immediately.
The danger of storing a Code Signing certificate in the PFX file was the main reason for the transition of all these certificates to token. Both the Code Signing OV and EV certificate must be stored on a token and its misuse in theft is virtually impossible; if the password is entered several times, the token is blocked.
Feel free to contact our Customer Support to help you choose certificate and ask any questions.
We are sorry that you did not find the required information here.
Please help us to improve this article. Write us what you have expected and not found out.